Proof-of-Work vs. Proof-of-Stake: Which Is Better?
Proof-of-work and proof-of-stake are the most popular algorithms to secure and manage a blockchain, but they both have trade-offs
Blockworks exclusive art by axel rangel
Proof-of-work and proof-of-stake are consensus mechanisms, or algorithms, that allow blockchains to operate securely. These consensus mechanisms keep blockchains secure by allowing only genuine users to add new transactions.
They work by making potential participants prove they have dedicated some resource, like money or energy, to the blockchain. This feature helps filter out those who may not be genuine or committed to the network. The main difference between proof-of-work and proof-of-stake is how they choose who can add transactions to the chain.
Quick facts:
- Proof-of-work and proof-of-stake are algorithms, also known as consensus mechanisms, that help blockchains synchronize data and remain secure.
- These algorithms determine which node (computer) in the network can add the next block of transactions to the chain.
- Both mechanisms have proven to be successful at maintaining blockchains, though they each have trade-offs.
What is proof-of-work?
Proof-of-work is a system where computers compete against each other to be the first to solve complex puzzles.
This process is commonly referred to as mining because the energy and resources required to complete the puzzle are often considered the digital equivalent to the real-world process of mining precious metals from the earth.
Nathaniel Popper’s book "Digital Gold" uses an analogy to describe proof-of-work in the Bitcoin system:
“It is relatively easy to multiply 2,903 and 3,571 using a piece of paper and pencil, but much, much harder to figure out what two numbers can be multiplied together to get 10,366,613.”
Using this analogy, we can imagine that a miner in Bitcoin’s network must figure out which two numbers can be multiplied to reach 10,366,613 by guessing combinations of numbers until it hits the correct answer. Once a computer determines that 2,903 can be multiplied with 3,571 to make 10,366,613, the computer presents the solution to the other computers in the network, which can easily verify that 2,903 and 3,571 do, in fact, equal 10,366,613 when multiplied.
When a miner solves this “puzzle” before other miners, they are allowed to create a new block (a grouping of transactions) and broadcast it to the network of nodes, which will then individually perform audits of the existing ledger and the new block. Should everything check out, the new block is "chained" onto the previous block, creating a chronological chain of transactions. The miner is then rewarded with bitcoins for supplying their resources (energy).
Proof-of-work, mining and security
Mining requires a great deal of electricity and secures the network by ensuring that only those that can prove they have expended resources are granted the right to append a new set of transactions to the blockchain.
Because of this feature, it is difficult, time-consuming and expensive to attack a proof-of-work system like Bitcoin’s. Attackers would need to purchase and set up mining equipment and pay for the electricity to run the equipment. They would then compete to solve the puzzle and attempt to add a block of transactions containing counterfeit bitcoins to the chain.
Should the nefarious miner successfully solve the puzzle first, they would try to broadcast a new block of transactions out to the rest of the network. The network’s nodes would then perform an audit to determine the legitimacy of the block and the transactions within it.
As the nodes audit the new block against the previous version of the ledger, they would notice the counterfeit bitcoins. The block would be considered invalid based on consensus rules.
Proof-of-work makes it impossible to counterfeit bitcoin unless a nefarious miner controls more than 50% of the entire network — this means they must control at least 51% of both the cumulative computing power of miners, known as the hashrate, and the nodes in the network. If they did control more than half of the network, the bad actor could broadcast a bad block to the network and have their nodes accept the block to the chain.
Given how large Bitcoin’s network has grown and how much energy miners contribute to the proof-of-work system, such an attack would be nearly impossible today.
If a government, company or other entity were to gather enough resources to successfully make up more than 50% of the network with the intention of attacking it, the network’s genuine participants would likely create a new branch of the chain, also known as a fork, rendering the previous chain and the attack against it useless.
What is proof-of-stake?
In the proof-of-stake system, validators (the proof-of-stake equivalent of miners) are chosen to find a block based on the number of tokens they hold rather than having an arbitrary competition between miners determine which node can add a block.
In this system, the “stake” amount, or quantity of crypto a user holds, replaces the work miners do in proof-of-work. This staking structure secures the network because a potential participant must purchase the cryptocurrency and hold it to be chosen to form a block and earn rewards.
Participants are required to spend money and dedicate financial resources to the network, similar to how miners must expend electricity in a proof-of-work system. Those who have spent money on coins to earn these rewards have a vested interest in the network's continued success.
Proof-of-stake prevents attacks and counterfeit coins with essentially the same mechanism as proof-of-work. Instead of controlling 51% of the mining hashrate and nodes, like with proof-of-work, attackers of a proof-of-stake system would need to hold at least 51% of the coin’s supply and control at least 51% of the network's nodes.
Pros and cons of proof-of-work and proof-of-stake
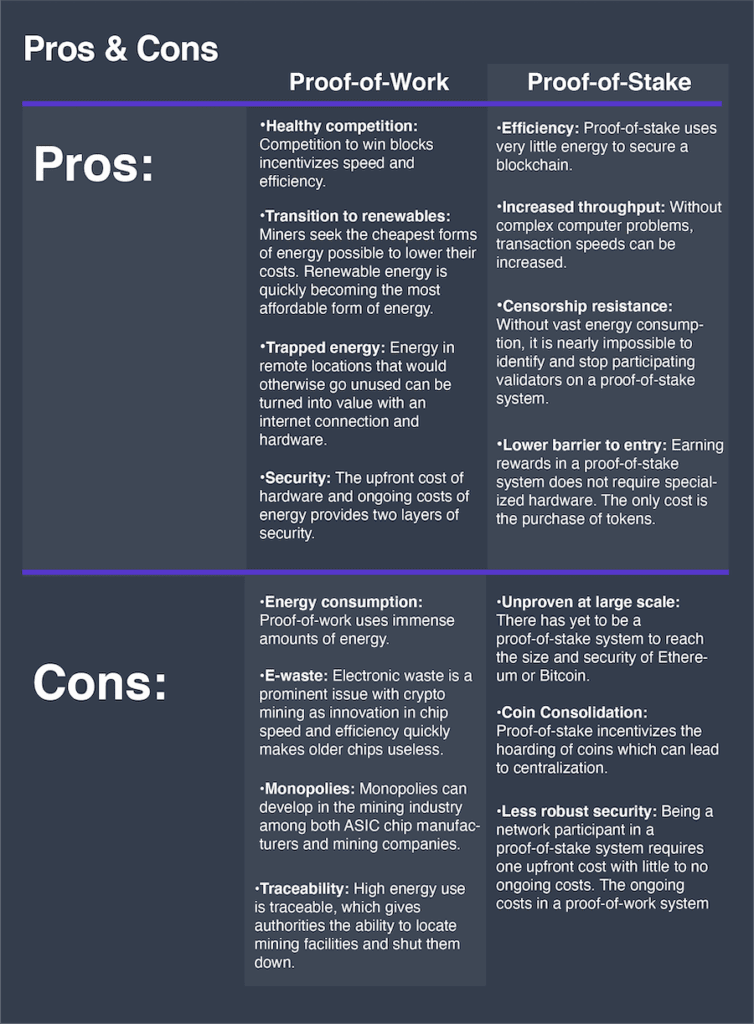
Proof-of-work pros, explained
Healthy competition and renewable energy
Competition in bitcoin mining is fierce. To lower their costs, mining companies constantly seek out the most efficient ways to mine. This process inherently rewards those who can find the cheapest forms of energy and come up with newer technology to create faster and more efficient chips for mining.
In addition to benefiting cryptocurrency mining, competition amongst chipmakers can result in breakthroughs in computer hardware that may carry over to other industries outside of crypto mining.
Trapped energy
Crypto mining allows some communities to harness their trapped energy and convert it into some form of value, which can then be transferred or used to fund other projects, ultimately generating economic activity in remote areas.
China’s Sichuan and Yunnan provinces are two real-world examples. These provinces have intense wet seasons that can produce enormous amounts of renewable hydroelectric power. Unfortunately, the provinces have no way of transporting and selling this energy to other areas.
The provinces began mining bitcoin to harness surplus energy and converted it to have tradeable value. In September 2019, China was responsible for over 70% of Bitcoin’s hashrate because of these cheap power sources. China later banned crypto mining as it sought to create its fiat digital currency. The move forced the massive exodus of miners to other areas where power is cheap. As a result, Kazakhstan became a mining hotspot alongside Iran and the United States.
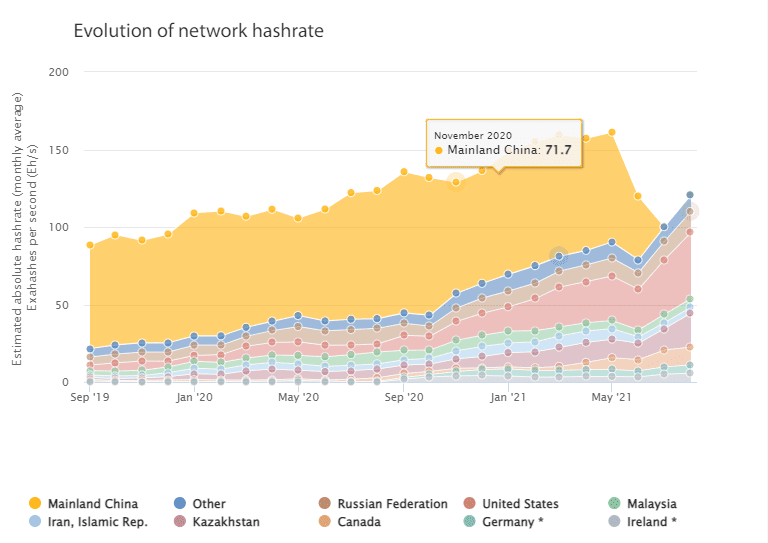 Share of Bitcoin’s hashrate by region. Source: Cambridge University
Share of Bitcoin’s hashrate by region. Source: Cambridge UniversitySecurity
So far, proof-of-work has been the most proven way to maintain consensus and security within a distributed public network. This is because proof-of-work requires the initial cost of hardware and the ongoing expenditure of resources, rather than a single upfront expense to participate like proof-of-stake.
Bitcoin was launched in 2009 and has had an over 99.98% uptime. As of writing, there have only been two instances of downtime: once in August 2010 and another in March 2013. These two incidents were solved with opt-in software updates to nodes — thanks to the consensus mechanism, network participants all decided these updates were in the best interest of the collective network.
Proof-of-work cons, explained
Energy consumption
Bitcoin and other proof-of-work blockchains, like Ethereum, consume significant amounts of energy to provide their security model to their networks. Bitcoin consumes more power than entire nations, including Ukraine and Norway. Environmentalists have argued that the practice is wasteful.
Rebuttal: While these systems consume massive amounts of energy, many critics fail to evaluate the types of energy used for mining and instead equate its high energy use to a large environmental footprint. However, studies have shown that bitcoin miners use various energy sources in their operations. Some estimates have shown renewable energy to be the dominant form used, ranging between 50% to over 70% of total power used.
It is important to note that many of these studies only report on mining companies and other operations that wish to participate in surveys.
E-Waste
Electronic waste may be the most valid criticism of the bitcoin network’s consumption of resources. Proof-of-work miners generally run at full power 24/7. Sometimes poor conditions like humidity, high temperatures and inadequate ventilation impact mining facilities and shorten equipment lifespan.
On top of that, ASIC chip manufacturers are constantly developing newer, more effective chips. When an innovation occurs, old chips become less effective at winning blocks than newer chips. Eventually, the older chips are phased out and become e-waste.
Rebuttal: Current ASIC mining chips typically last between three to five years. While new chips eventually replace older chips, they are likely to last longer as they become more efficient and resistant to high temperatures and prolonged hashing.
Traceability
Censorship and traceability are other crypto mining concerns, which have already occurred in places like China, where cryptocurrency mining was banned. The immense power draw can be located using electricity readings or even thermal cameras. The ability to trace where crypto mining takes place allows anti-crypto regimes to crack down on the practice.
If a nation were to allow mining only for those who have secured some type of license, it could undermine decentralization by not allowing the network to be completely public.
Rebuttal: Outside of China, nations around the world seem to be pro-crypto in some capacity. Some countries may seek to regulate mining. However, as long as miners can still operate in remote areas, it should help to prevent monopolization and censorship.
Proof-of-stake pros, explained
Efficiency
Proof-of-stake systems are significantly more energy-efficient than proof-of-work operations. The hardware requirements of many proof-of-stake systems are equivalent to average laptops on today’s market. Validator software is also not very demanding across most proof-of-stake systems.
Increased throughput
In proof-of-stake, validators are chosen to find a block based on how many tokens they hold, rather than a competition among miners to solve a puzzle. The time it takes for the proof-of-stake algorithm to choose a validator is significantly quicker than the proof-of-work competition, allowing for increased transaction speeds.
While this is true, all blockchains — whether they are proof-of-stake or not — are slowed by the process of nodes reaching a consensus after a validator broadcasts the newly found block to them.
Censorship resistance
Unlike proof-of-work, which requires lots of energy and a significant physical presence, proof-of-stake validators can be running on small laptops. This means that a single validator controlling a third of a globally distributed monetary network could operate in the corner of a coffee shop rather than a warehouse filled with thousands of humming computers.
Lower barrier to entry
Proof-of-stake validators only need to spend money once to participate — they must buy tokens to win blocks in the proof-of-stake model. In contrast, a miner in a proof-of-work system must purchase mining equipment and keep it running indefinitely, incurring energy costs that can fluctuate. This allows more individuals to participate who otherwise wouldn't be able to.
Proof-of-stake cons, explained
Unproven at large scale
A proof-of-stake system has yet to scale to the size of Bitcoin or Ethereum. For this reason, proof-of-stake systems are not yet as decentralized or secure as leading proof-of-work systems.
Rebuttal: While proof-of-stake systems have not yet become the size of networks like Bitcoin’s, there is no reason they cannot with time. Proof-of-stake systems may have the potential to scale beyond what proof-of-work systems are capable of, given that there is a lower barrier to entry and specialized hardware is not required to run them.
Coin consolidation
Consolidation of coins among only a few validators is the most common argument against proof-of-stake systems. The nature of proof-of-stake incentivizes the accumulation of coins to increase the chance of winning a block and receiving a reward.
Token markets can be cornered by an entity with deep pockets, allowing them to amass a majority of tokens. Most proof-of-stake systems let single entities create any number of validators, and because there is little upfront financial cost to create validators, someone who controls the majority of tokens could control the majority of the network.
This makes the initial distribution of proof-of-stake coins extremely important. Some newer proof-of-stake coins sell tokens to investors before they’re publicly available. In some cases, these token sales have made up 40% or more of max token supplies giving venture capital firms and other early investors a considerable advantage over others in earning network rewards.
Rebuttal: It’s true that proof-of-stake chooses block creators mainly by the size of their stake, but some blockchains are already beginning to implement methods to reduce this risk of centralization. Some are including a degree of randomization and factors such as “coin age,” or how long the stake has been held, to the selection algorithm. This ensures that stake size isn’t the only factor in determining block formation and that smaller validators have a chance of winning.
Some blockchains have structured their systems so that validators who surpass a certain threshold of coins begin receiving fewer rewards. This incentivizes stakers to delegate their stake to smaller validators, helping spread tokens across more validators, increasing decentralization and security.
Less robust security
As mentioned above, having a lower barrier to entry for network participants can help increase validator count and, by extension, decentralization, but making it easier to become part of the network can also decrease its security.
Should a bad actor seek to attack a proof-of-work network, they would need to buy enough hardware to represent the majority of the network, and then they would need to pay to run it all. The two-fold security system of the initial cost of equipment and the ongoing energy costs makes attacking the network less realistic. Proof-of-stake systems only have initial upfront costs to participate, leaving them more open to attack.
Bitcoin’s current hashrate is nearly 200 million terahashes per second. Bitmain’s top-of-the-line ASIC miner, the S19J, can do 88 terahashes per second. By that measure, it would take roughly 1.2 million of these chips to make up just half of Bitcoin’s network. The current price of this ASIC is $10,390 per unit, meaning it would cost roughly $12.5 billion to purchase enough miners to make up half of Bitcoin’s network, only to then pay enormous fees to run the machines.
In contrast, if a nefarious actor wished to attack a proof-of-stake chain, take Avalanche for example, they would need to buy over half the tokens (roughly $19 billion at current prices) and set up enough validators to make up over half the network (630 validators at Avalanche’s current validator count). Because proof-of-stake validators don’t necessarily require expensive hardware or tons of energy to run, attackers only incur the upfront cost of purchasing tokens rather than ongoing energy costs.
Rebuttal: The initial upfront cost to attack a proof-of-stake network of sufficient size is becoming large enough that the issue of not having ongoing costs is slowly becoming irrelevant. For example, becoming the majority stake in Avalanche already requires nearly $20 billion at today’s prices. The more popular these blockchains become and the more holders of a proof-of-stake network’s coin there are, the harder it is to attack it.
Frequently asked questions
What is proof-of-work?
Proof-of-work is a tool that secures a blockchain and helps it maintain accurate information (transactions). Computers (nodes) in the system race to see who can solve a complex puzzle first. Winners of this race are then allowed to add a new block of transactions to the chain. This puzzle takes large amounts of costly energy to solve, ensuring participants are more likely to be genuine. Those who win are rewarded with bitcoin.
What is a bitcoin miner?
A bitcoin miner is a computer that participates in the competition to solve puzzles in proof-of-work blockchains. They use large amounts of energy in this process and are rewarded with bitcoin when they beat everyone else in solving the puzzle. It is called mining because the energy and resources required are often considered the digital equivalent to the real-world process of mining precious metals from the earth.
Check out our explainer for more info on the profitability and economics of bitcoin mining.
What is proof-of-stake?
Proof-of-stake is a tool to secure a blockchain and help it maintain accurate information. It uses an algorithm that chooses who can add the next block of transactions to the chain based on how many tokens are held.
What is a validator in proof-of-stake?
A validator is the proof-of-stake equivalent of a miner in proof-of-work. Validators are nodes in a blockchain network that “stake” or pledge their tokens to the network. Validators are chosen to create new blocks of transactions based on how many tokens they hold. Other token holders who are not validators can delegate their holdings to a validator to get a share of rewards a validator earns when they are chosen to create a new block of transactions.






